
Strengthen the defense line of network security
- Categories:NEWS
- Author:
- Origin:
- Time of issue:2019-05-08 10:35
- Views:
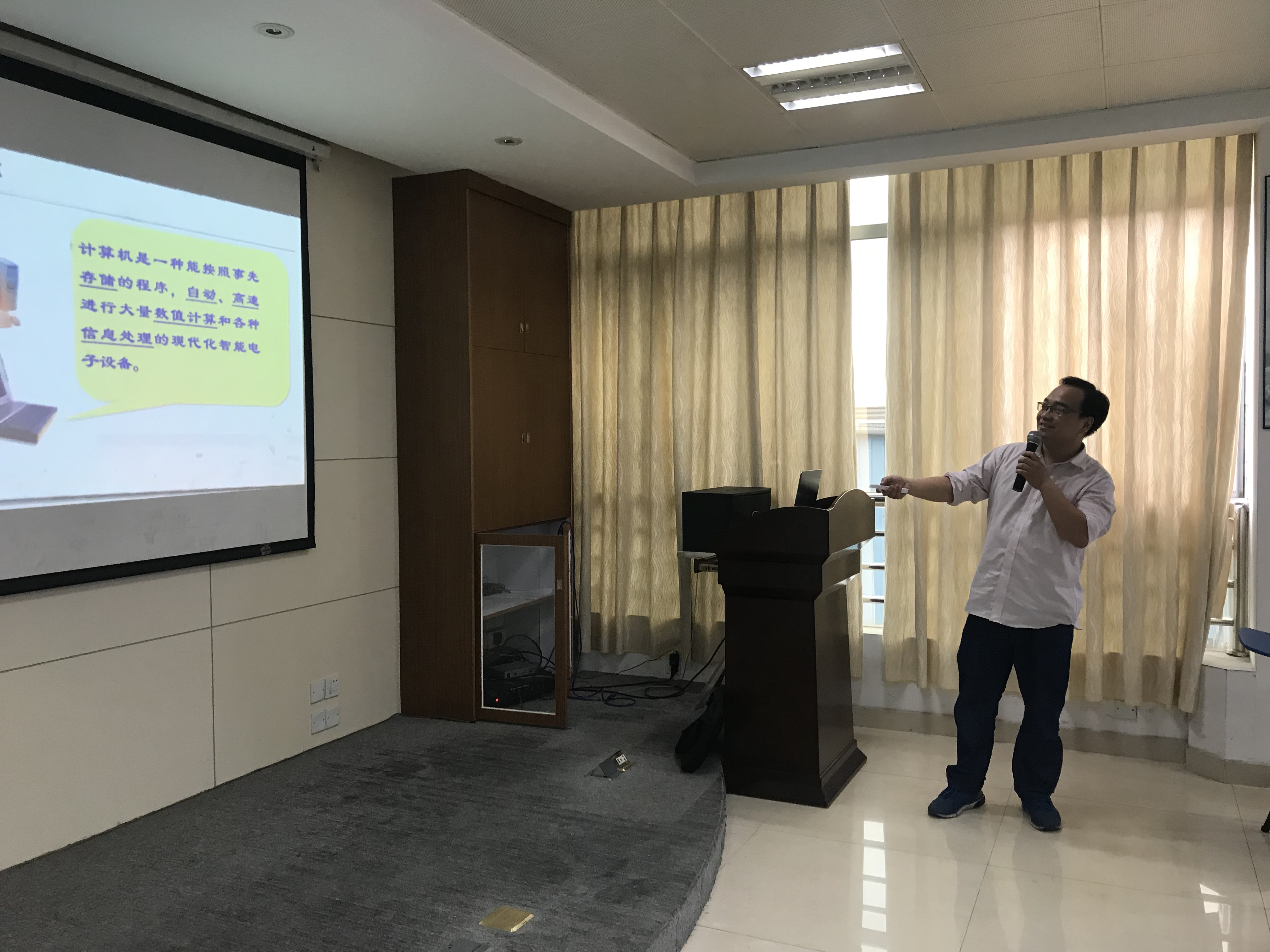
(Summary description)Jinbangcompanytostrengthennetworksecuritytraining Nearfuture,jinbangcompanynetworksystembreakdown,suspectsuffersvirusattack,afterinvitingprofessionalpersonagetofightcontinuously,eliminatedthebreakdownfinally.Inordertoimprovenetworksecurityawarenessandstrengthennetworksecuritywork,thecompanyorganizedanetworksecuritytrainingonMay3. TrainingbytheadministrationdepartmentHuXianshengspeaker,hislectureonthetopicof"computercultureandnetworkdefense",thecoursefromthehistoryofcomputer,networkdefense,computerhardwareandotheraspects,explainedthedevelopmenthistoryofcomputer,computervirusattackmeans,howtodonetworksecurityaspectsofknowledge,thehackerwarbetweenChinaandJapan,inthehistoryofthebesthackers,QQ'knowledgelearning,etc.Althoughsomeprofessionalknowledgewasdifficulttounderstandinthewholeclass,duetothecarefulpreparationofthelecturer,illustrated,deepintothesimple,theaudiencestillreportedalotofdrygoods,learnedalotofknowledge. Employeesfromadministrationdepartment,humanresourcesdepartment,productiondepartment,purchasedepartmentandotherdepartmentswithadesireforcomputerknowledgeparticipatedinthetraining.KnowledgesharingEnterpriseinformationsecuritymethodsandskills: 1.Enhanceemployees'awarenessofinformationconfidentiality.Atpresent,manyenterpriseemployeesaremistakenaboutinformationsecurity.Trytouseacomplexpasswordforprotection,ratherthanjustasimplepassword,suchas"123456"differentaccountsandfiles,setupdifferentpasswords,soasnottoallowintrudersor"leaker"opportunities.However,manyenterprisesdonotinvolveinformationsecurityandconfidentialityintheorientationtraining.Thelackofinformationsecurityandconfidentialityawarenessofemployees,enterprisesalsohaveacertainresponsibility. 2.Onlinebehaviormanagementandcontrol.Employees'safeonlinebehaviorisbecomingmoreandmoreimportantforenterprisedataandinformationsecurity,whichisalsoanimportantreasonforthegradualexpansionofmarketdemandforonlinebehaviormanagementproductsintheinformationera.Enterprisesuseappropriateonlinebehaviormanagementproducts,guideemployeestosafetyonline,isboundtogreatlyprotectthesecurityofenterpriseinformation. 3,firewall,antivirussoftwareinstallation.ThedevelopmentoftheInternettodaymakesitimpossibleforenterprisestoconductnegotiationsinvariousaspectswithoutusingtheInternet.ItisbecauseoftheopennessoftheInternetthatenterpriseinformationmaybeexposedtothevastnumberofInternetusersatanytime.Therefore,inthemanagementoftheinternalnetworkatthesametime,alsoneedtocontrolthebehavioroftheexternalnetwork,timelyupdatethefirewall,anti-virussoftwareversion,doagoodjobofcomputernetworkprotection,isalsoanimportantmeanstopreventcorporateinformationtheft. 4.Useencryptionsoftwaretoencryptenterpriseinformationanddocuments.Strengtheningemployees'safetyawareness,installingonlinebehaviorcontrolsoftware,installingfirewallandanti-virussoftwarearealleffectivemeanstopreventcorporateinformationdisclosure,butthesearenotenough.Therefore,itisnecessaryforustoprotecttheinformationsecurityofcompaniesmoreeffectivelythroughencryptionsoftware.Atpresent,thedomesticencryptionsoftwareindustrystandardshavenotbeenestablished,thechoiceoftransparentencryptionsoftwaremanufacturersneedtobecareful,shouldbefromtheenterpriseresearchanddevelopmentstrength,thesecurityofthesoftwareitself,therecoveryofencrypteddataandthestabilityandcompatibilityofthesoftwareandeasytooperatetheseaspectstoconsider. Wewillholdmorewonderfultrainingcoursesinthecomingdays!!
Strengthen the defense line of network security
(Summary description)Jinbangcompanytostrengthennetworksecuritytraining Nearfuture,jinbangcompanynetworksystembreakdown,suspectsuffersvirusattack,afterinvitingprofessionalpersonagetofightcontinuously,eliminatedthebreakdownfinally.Inordertoimprovenetworksecurityawarenessandstrengthennetworksecuritywork,thecompanyorganizedanetworksecuritytrainingonMay3. TrainingbytheadministrationdepartmentHuXianshengspeaker,hislectureonthetopicof"computercultureandnetworkdefense",thecoursefromthehistoryofcomputer,networkdefense,computerhardwareandotheraspects,explainedthedevelopmenthistoryofcomputer,computervirusattackmeans,howtodonetworksecurityaspectsofknowledge,thehackerwarbetweenChinaandJapan,inthehistoryofthebesthackers,QQ'knowledgelearning,etc.Althoughsomeprofessionalknowledgewasdifficulttounderstandinthewholeclass,duetothecarefulpreparationofthelecturer,illustrated,deepintothesimple,theaudiencestillreportedalotofdrygoods,learnedalotofknowledge. Employeesfromadministrationdepartment,humanresourcesdepartment,productiondepartment,purchasedepartmentandotherdepartmentswithadesireforcomputerknowledgeparticipatedinthetraining.KnowledgesharingEnterpriseinformationsecuritymethodsandskills: 1.Enhanceemployees'awarenessofinformationconfidentiality.Atpresent,manyenterpriseemployeesaremistakenaboutinformationsecurity.Trytouseacomplexpasswordforprotection,ratherthanjustasimplepassword,suchas"123456"differentaccountsandfiles,setupdifferentpasswords,soasnottoallowintrudersor"leaker"opportunities.However,manyenterprisesdonotinvolveinformationsecurityandconfidentialityintheorientationtraining.Thelackofinformationsecurityandconfidentialityawarenessofemployees,enterprisesalsohaveacertainresponsibility. 2.Onlinebehaviormanagementandcontrol.Employees'safeonlinebehaviorisbecomingmoreandmoreimportantforenterprisedataandinformationsecurity,whichisalsoanimportantreasonforthegradualexpansionofmarketdemandforonlinebehaviormanagementproductsintheinformationera.Enterprisesuseappropriateonlinebehaviormanagementproducts,guideemployeestosafetyonline,isboundtogreatlyprotectthesecurityofenterpriseinformation. 3,firewall,antivirussoftwareinstallation.ThedevelopmentoftheInternettodaymakesitimpossibleforenterprisestoconductnegotiationsinvariousaspectswithoutusingtheInternet.ItisbecauseoftheopennessoftheInternetthatenterpriseinformationmaybeexposedtothevastnumberofInternetusersatanytime.Therefore,inthemanagementoftheinternalnetworkatthesametime,alsoneedtocontrolthebehavioroftheexternalnetwork,timelyupdatethefirewall,anti-virussoftwareversion,doagoodjobofcomputernetworkprotection,isalsoanimportantmeanstopreventcorporateinformationtheft. 4.Useencryptionsoftwaretoencryptenterpriseinformationanddocuments.Strengtheningemployees'safetyawareness,installingonlinebehaviorcontrolsoftware,installingfirewallandanti-virussoftwarearealleffectivemeanstopreventcorporateinformationdisclosure,butthesearenotenough.Therefore,itisnecessaryforustoprotecttheinformationsecurityofcompaniesmoreeffectivelythroughencryptionsoftware.Atpresent,thedomesticencryptionsoftwareindustrystandardshavenotbeenestablished,thechoiceoftransparentencryptionsoftwaremanufacturersneedtobecareful,shouldbefromtheenterpriseresearchanddevelopmentstrength,thesecurityofthesoftwareitself,therecoveryofencrypteddataandthestabilityandcompatibilityofthesoftwareandeasytooperatetheseaspectstoconsider. Wewillholdmorewonderfultrainingcoursesinthecomingdays!!
- Categories:NEWS
- Author:
- Origin:
- Time of issue:2019-05-08 10:35
- Views:
Jin bang company to strengthen network security training

Knowledge sharing
Enterprise information security methods and skills:
We will hold more wonderful training courses in the coming days!!

ADDRESS: NO. 38, FENGXIANG ROAD, DALIANG, SHUNDE DISTRICT, FOSHAN CITY, GUANGDONG PROVINCE
TEL:0757-22213007/22227324
FAX:0757- 22229013

LEARN MORE ABOUT IT
GUANGDONG JINBANG PLASTIC PACKAGING CO., LTD. 粤ICP备11066138号-1 POWERBY:300.CN MANAGER
TEL:0757-22319618 ADDRESS: NO. 38, FENGXIANG ROAD, DALIANG, SHUNDE DISTRICT, FOSHAN CITY, GUANGDONG PROVINCE